Govern every identity, automate every review
AI-powered identity governance. Onboard apps faster, review smarter, enforce continuously — across human, non-human, and agentic identities.
Traditional IGA tools take weeks to onboard a single application and produce review campaigns so large that reviewers rubber-stamp them.
SlashID takes a fundamentally different approach: an AI agent handles application onboarding end-to-end, the access graph provides full context for every review decision, and policy-driven automation enforces governance continuously across the entire identity lifecycle.
Onboard apps in minutes
AI agent discovers entitlements, maps roles, and configures connectors automatically. Reduce weeks of manual configuration to minutes.
Review what matters
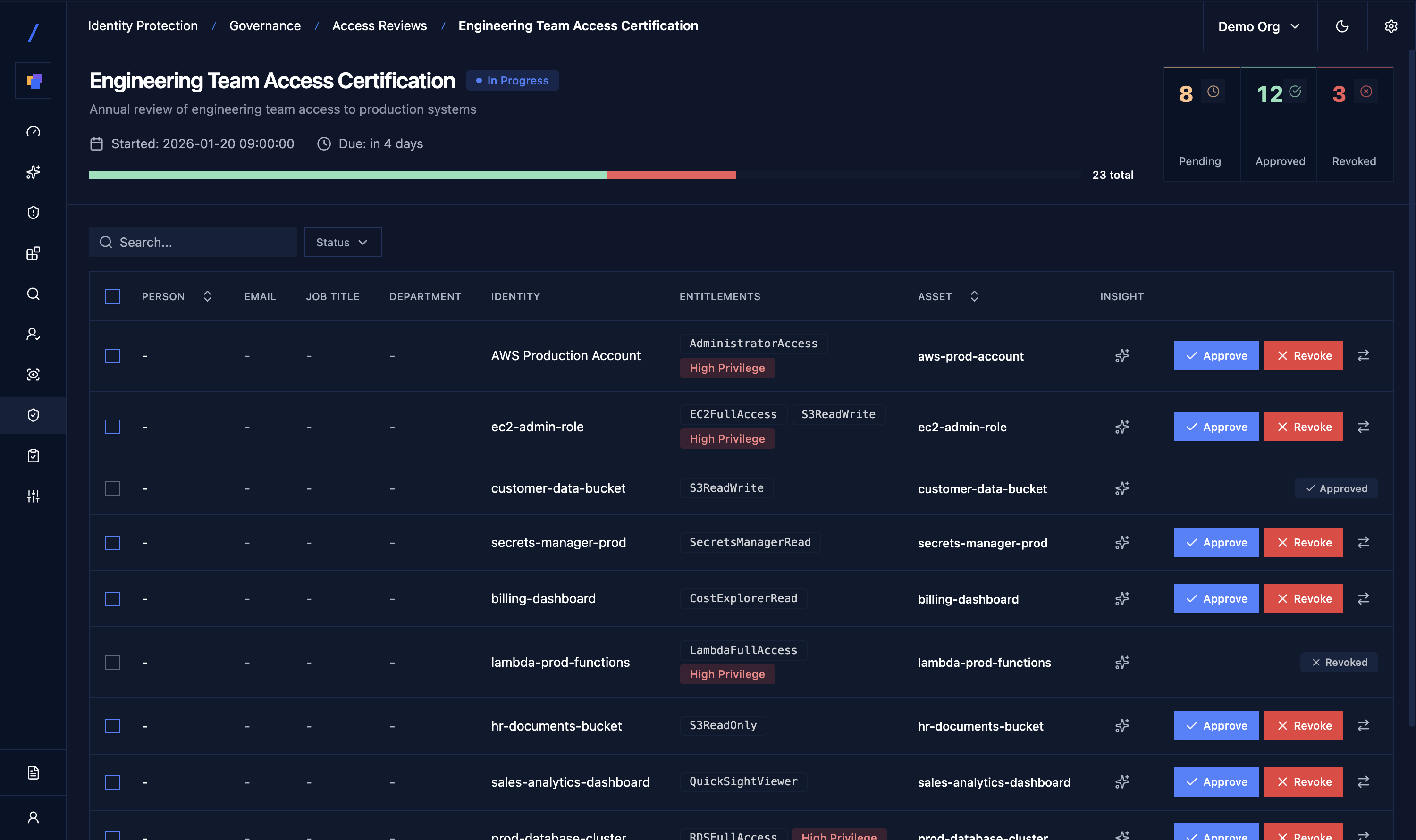
AI prioritization using runtime data and access graph context eliminates review fatigue. Reviewers focus on decisions that carry real risk.
Enforce continuously
Policy-based onboarding and offboarding across all identity types. Define rules once — access granted, adjusted, or revoked automatically.
Benefits
How it helps
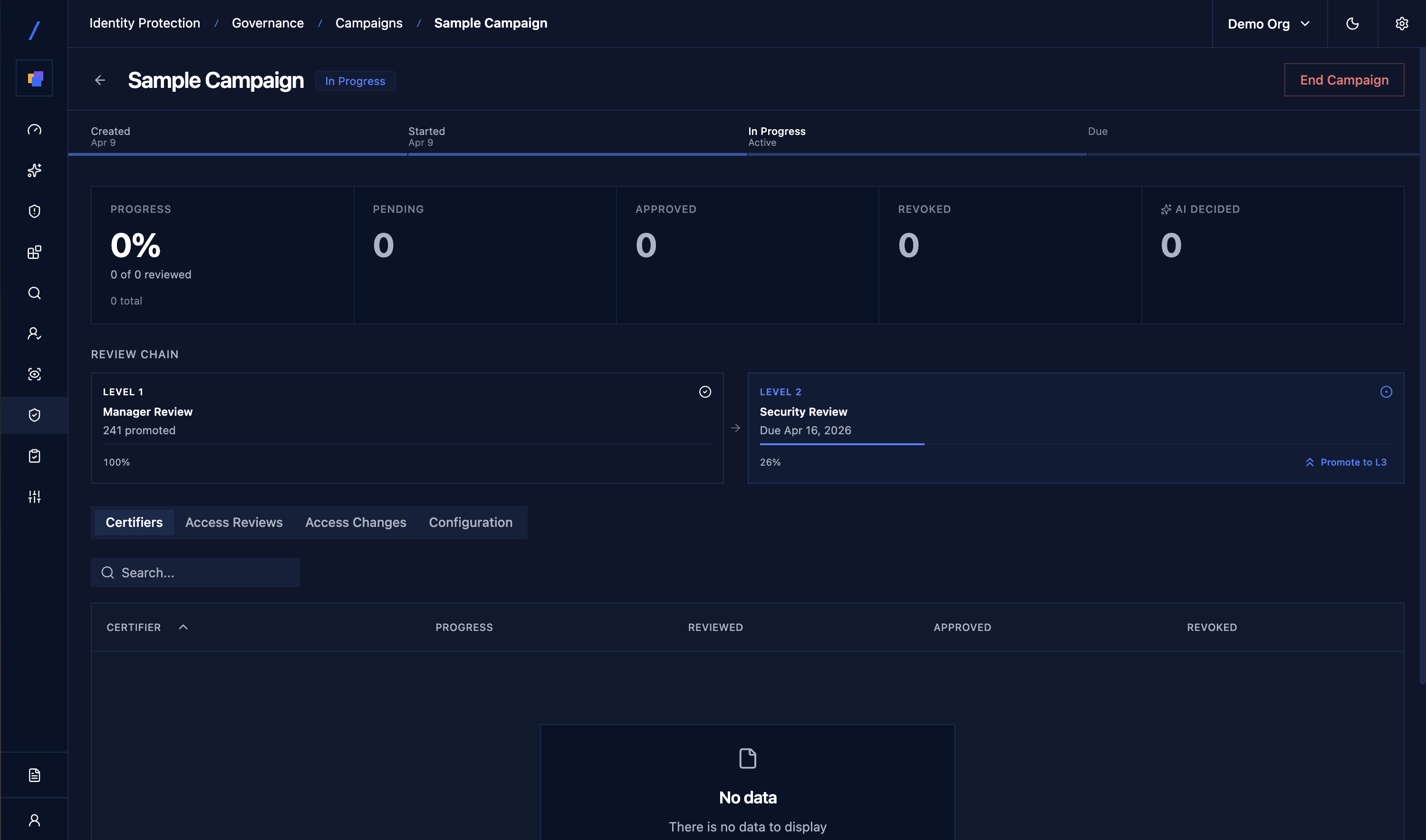
AI-driven access reviews
Replace manual reviews with AI-prioritized campaigns. Runtime behavioral data and access graph context surface the entitlements that carry real risk — excessive permissions, dormant accounts, toxic combinations. Reviewers approve or revoke in seconds, not hours.
Automated app onboarding
The AI agent discovers entitlements, maps roles, and configures connectors — reducing weeks of setup to minutes. It continuously adapts as your application landscape evolves, so new apps are governed from day one without manual integration work.
Flexible campaign populations
Full customizability via the access graph. Slice review populations by department, application, risk score, identity type, or any graph attribute. Run targeted campaigns instead of boiling-the-ocean enterprise-wide reviews.
Policy-based lifecycle automation
Define onboarding and offboarding policies once. Access is granted on day one, adjusted on role change, and revoked on departure — automatically, with full audit trail. Consistent governance for joiners, movers, and leavers.
Governance for all identity types
Unified lifecycle management for human employees, non-human identities (service accounts, API keys), and agentic identities (AI agents, autonomous systems). One governance model, not three.
Resource & identity-based reviews
Support both perspectives: review all identities accessing a resource, or all resources an identity can reach. Choose the lens that fits your compliance objective.
Easy to deploy
How it works
Read-only connectors pull identity and entitlement data from IdPs, cloud providers, SaaS, on-prem, and databases.
The AI agent maps entitlements, roles, and resources from every connected application — automatically and continuously.
Launch targeted campaigns scoped by any graph attribute. Reviewers see full context — last activity, usage patterns, risk score, blast radius — alongside each decision.
Approved changes execute automatically. Generate audit-ready reports for PCI-DSS, SOC 2, ISO 27001, HIPAA, and custom frameworks on demand.
Unique Product Core
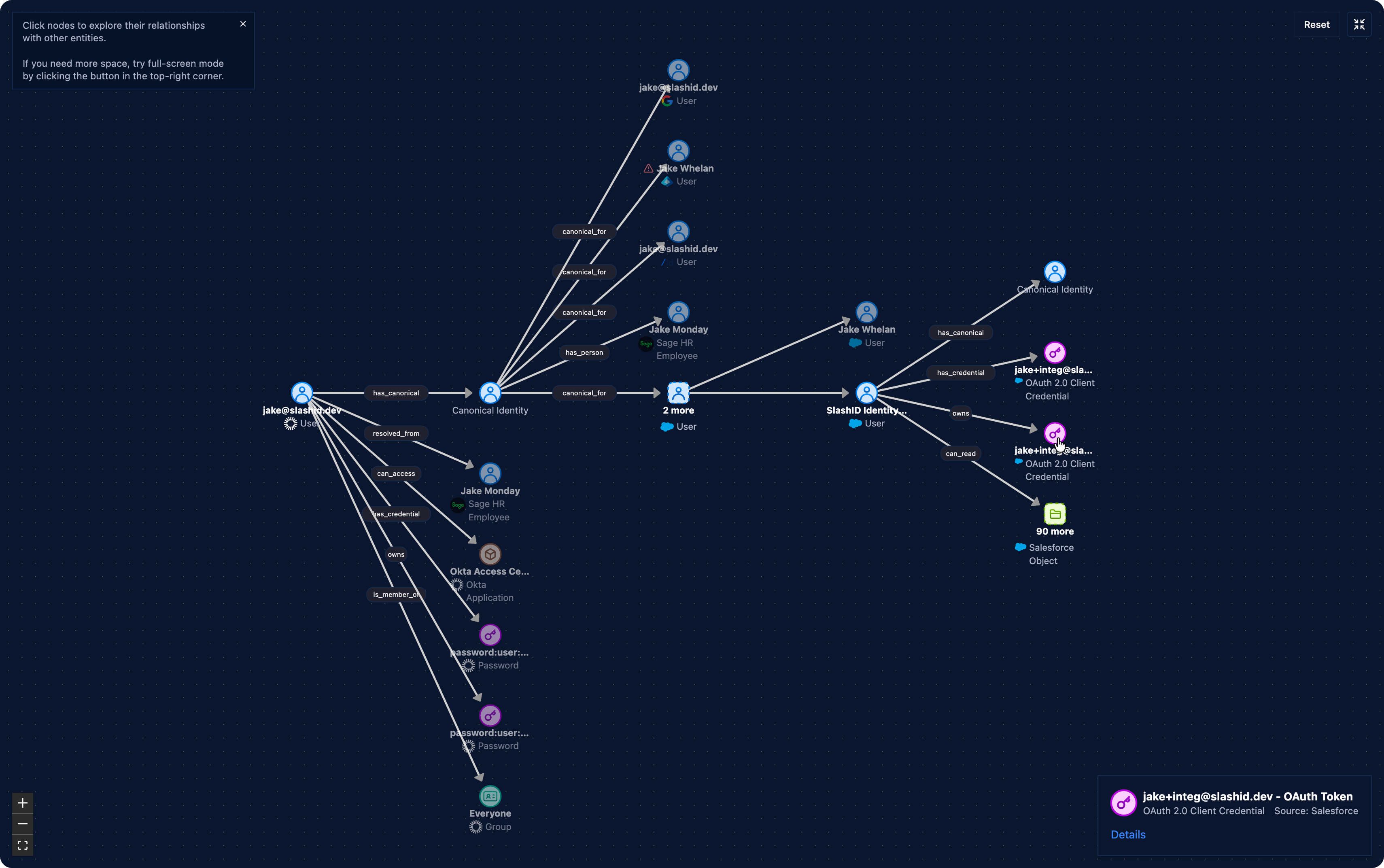
Access Graph Engine
- Unified identity graph — humans, services, AI agents, every resource
- Full campaign customizability: slice by dept, app, risk, or any graph attribute
- Resource-based and identity-based review modes
- AI-Assistant for natural language queries
AI-Powered Automation
- AI agent onboards apps — discovers entitlements, maps roles, configures connectors
- Review prioritization using runtime data + access graph context
- Policy-based onboarding and offboarding across the full lifecycle
- Supports human, non-human, and agentic identities