On February 6, 2026, NYDFS issued an industry letter warning DFS-regulated entities about a spike in targeted vishing attacks where threat actors impersonate IT help desk staff to steal credentials and MFA codes and gain remote access.
This post breaks down the technical mechanics of the campaign, why it reliably bypasses “MFA on paper,” and how to detect and contain it using identity telemetry — specifically mapping the NYDFS recommendations to SlashID Identity Protection, and MITM detection.
1. Attack anatomy: why this vishing flow works?
NYDFS describes a consistent pattern: attackers call employees on work/personal numbers (Impersonation), direct them to a malicious link (Social Engineering), capture credentials in real time, and then prompt for the MFA code to immediately authenticate and obtain remote access.
A more technical view of the kill chain
Phase A — After the reconnaissance phase, where enterprise information is gathered and enumerated, attackers attempt to gain an initial foothold by authenticating via out-of-band channels using various techniques like Help Desk Impersonation, SMS and vishing, and SIM swapping.
Phase B — Foothold Establishment — by using compromised credentials, and SSO access using a legitimate account (potentially enabling lateral movement across the environment).
Phase C — MFA bypass. The expression “Attackers don’t hack, they log in” is becoming more and more relevant. Even strong MFA can be defeated indirectly if the attacker can force account recovery, enroll a new device, or abuse help desk reset processes. The root cause of MFA bypass is the ability to replay tokens (SAML, OAuth) before they are expired.

It seems that the same attack vector SlashID previously analyzed in the Scattered Spider breaches at MGM and Caesars is not only still relevant today, but has become even more sophisticated.
2. How SlashID helps to detect and prevent
A vishing compromise leaves a very “identity-shaped” trail. The most actionable signals are not the phone call - they’re the sequence of identity events. High-signal detection patterns:
- Password reset → new login from new geo/device within minutes
- New MFA device enrolled shortly after reset
- SSO session minted from a new IP / ASN, then immediate access to high-value apps
- Privilege escalation attempts after initial foothold
SlashID is structured around two main ideas:
- Ingest identity posture + event logs from the sources (IdP, cloud, AD/Entra, SaaS), and
- Run a detection engine that emits threat detections and posture detections.
| Attack Phase | How the Attacker Exploits | How SlashID Detects | How SlashID Prevents |
|---|---|---|---|
| Recon & Initial Foothold | Impersonates IT Help Desk via phone call (vishing) or SMS | N/A (The phone call itself occurs outside the identity plane). | Browser Extension + TOTP Verification |
| Credential Harvesting & MFA Interception | User visits a fake login page (often a reverse proxy like Evilginx). Attacker captures credentials and the MFA code as the user types them. | MITM Token Detection | TOTP Verification |
| Lateral Movement & Impact | With a valid SSO session, the attacker accesses file shares, or internal tools to exfiltrate data. | Identity Graph Analysis | AI Assistant & Queries |
These detection and response methods are discussed in more details in the following chapters.
2.1. Visibility Foundations and Detection Types that match vishing outcomes
SlashID typically ingests two types of data from each integrated data source such as Identity Data (users, NHIs, roles, permissions) and Events (activity logs showing how identities are used).
On the other hand, SlashID detection events include:
- Threat detection — Indicators of attack (IOAs)
- Posture detection — Misconfigurations (e.g., MFA disabled)
- Detection functions — CredentialStuffingAttempt, FederationBypass, MissingMFA
- Confidence score — Machine Learning model with a value between 0 and 1 indicating the likelihood that the detection is a true positive
- MITRE mapping fields — Automatic mapping to MITRE ATT&CK framework
Thus, providing continuous monitoring and detection.
2.2. Mutual TOTP for Help Desk vishing
The defining weakness of help desk vishing is that the call itself becomes the “authentication channel” as shown in the table above. Attackers win by convincing an agent to reset credentials / enroll MFA / approve recovery without a cryptographic way to verify who is on the other end of the line.
Mutual TOTP changes that: instead of trusting a voice, both parties perform a two-way verification handshake where each side must prove possession of a registered device (the verification is biometric-protected). It uses 6-digit RFC 6238 codes, rotating every 30 seconds, with bidirectional verification, real-time synchronization, and a 2-minute timeout.
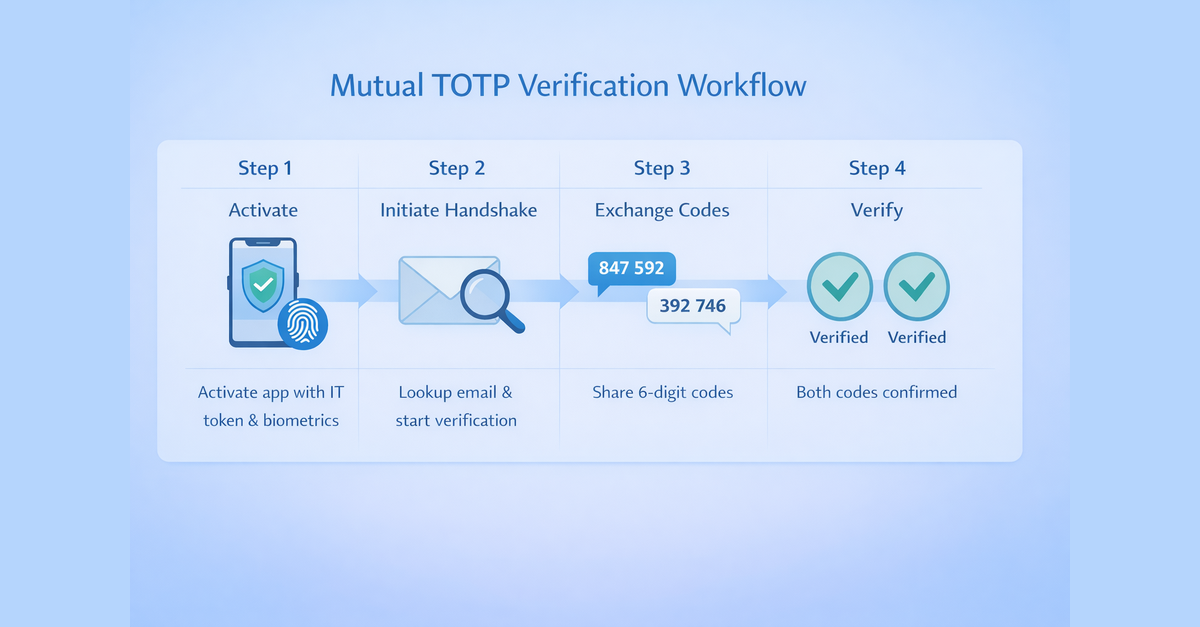
Operational model:
- Employee and help desk agent are both enrolled (activated with an IT token; access protected by FaceID/TouchID).
- One party initiates a handshake
- Both sides receive unique 6-digit TOTPs and read them to each other over the call.
- The handshake is marked Verified only when both codes are confirmed
Mutual TOTP blocks the “operator-assisted MFA bypass” moves because the attacker cannot complete the handshake without the registered device — thus, voice cloning/deepfakes won’t help.
2.3. Browser extension for phishing detection
SlashID also provides a browser extension that performs real-time phishing detection and identity protection at the client layer. While mutual TOTP secures the phone call, the browser extension secures the link click — the other critical hinge point in vishing campaigns.
SlashID’s browser extension is positioned to stop phishing where it happens: in the browser, before credentials are submitted. It inspects pages as they load by evaluating DOM, URL reputation, and form behavior, then a policy layer makes a decision (brand impersonation, typosquats, risky flows), and the extension can warn/block submission, or trigger extra authentication.
2.4. Detecting fake login attempts and MITM phishing
The vishing flow depends on redirecting victims to a malicious login page. SlashID provides an explicit MITM (reverse proxies) detection mechanism: you generate a MITM token tied to allowed domains, embed it in pages, and SlashID can detect when login pages are being accessed via unauthorized domains/proxy contexts. This is a strong fit for SSO login pages such as Okta or Entra.
2.5. Query the identity graph to confirm blast radius quickly
SlashID Identity Protection exposes your identity environment as a graph (identities, credentials, groups, policies, resources, and the relationships between them). By leveraging Cypher queries, security teams can quickly answer who has access to what, how did they get it, and what changed recently — which is exactly what you need during incidents like help desk vishing.
SlashID implements some high-value quality query patterns used to identify overprivileged identities, detect privilege escalation attempts, discover NHIs with unrestricted access to resources, and analyzing blast radius by identifying federated access risks.

For deeper investigations, analysts can leverage SlashID’s AI assistant to generate natural-language queries that surface risky access patterns, privilege escalation, or lateral movement paths.
3. A concrete NYDFS-aligned control map using SlashID
NYDFS latest industry letter guidance focuses on preventing credential theft, strengthening MFA controls, and monitoring identity activity for signs of compromise. SlashID maps directly to these requirements by combining identity telemetry, phishing detection, and automated remediation to detect and contain vishing-driven account takeovers.
| NYDFS Control Requirement | How SlashID Helps |
|---|---|
| Identity Verification Procedures (not caller ID) | Monitor password reset and MFA enrollment events; trigger detection webhooks for suspicious identity changes and automate containment |
| Strengthen MFA controls and enrollment permissions | Detect MFA posture gaps (e.g., MissingMFA), enforce stronger authentication workflows, and enable SlashID’s TOTP |
| Continuous monitoring of authentication activity | Correlate identity telemetry across sources and query the identity graph to identify privilege escalation or unusual access patterns (e.g., FederationBypass) |
| MFA must be continuously evaluated | Use posture detections and continuous assessments to validate MFA coverage and flag configuration drift |
| Reduce exposure to fake login portals | Deploy MITM token detection on authentication surfaces to detect malicious login proxies and phishing infrastructure |
Conclusion
Help desk vishing attacks show how modern intrusions increasingly target identity workflows rather than technical vulnerabilities. By exploiting social engineering and weak identity verification processes, attackers can obtain legitimate access and bypass traditional defenses.
SlashID helps break this attack chain by combining identity telemetry, behavioral detections, phishing protection, and identity graph analysis to detect suspicious authentication patterns and quickly contain compromised accounts. By implementing identity-centric security controls with SlashID, organizations can significantly reduce the risk of vishing-driven account takeovers and stop attackers before they can expand their foothold.
If you’re looking to strengthen your defenses against vishing attacks, contact SlashID to learn how our platform can help protect your organization.



